Learning about Mobile App Security

I love technology and everything related, from gadgets to new professional techniques. I like thinking, researching, optimizing, inventing and developing. I have a strong background in software research and development, operating systems, Voice-over-IP, network security, wired and wireless network engineering, complemented with electronic engineering background.
My career goal is to always keep learning, to be challenged, and to work remotely so I can be present for my family.
Bug hacker and master troubleshooter, my strength is understanding a problem and getting to the root of it. I'm mostly a self-taught individual and a constant learner. I push my technical boundaries daily and search for ways to improve my skills every day. With over 20 years of experience writing software in various languages, creating or optimizing algorithms, the digital development world is my turf.
Sample challenges which I particularly enjoyed:
- Created a GLSL based magnification tool for a client who was turned down by three other companies as "impossible to do on macOS".
- Optimized several SQL queries to reduce load time of a particular web page from several seconds to sub 50ms.
- Identified the root cause of stuttering animations in iOS mobile app and implemented mitigation strategy
Specialties: Swift, Objective-C and PHP Software Development; TCP/IP and Wireless Network Engineering
For mobile security, there are a few companies offering courses/certification but they are fairly expensive. Security Compass, and Secure Code Warrior, would be my recommendations if you want to go that way. The community is split on whether that experience was positive for them.
If you want to study on your own, make sure you understand Symmetric and Asymmetric cryptography, how to use CryptoKit, how to encrypt/decrypt files using AES GCM, how to sign and verify signature of data using P256, how to generate a symmetric key using asymmetric keys using P256 ECDH key derivation.
You will also want to understand how to use Apple's TouchId and FaceID, how to use the SecureEnclave, the Keychain.
Make sure you know how to enable iOS file protection when writing files to disk (NSFileProtectionComplete) and how you can also set this by default using App Entitlements.
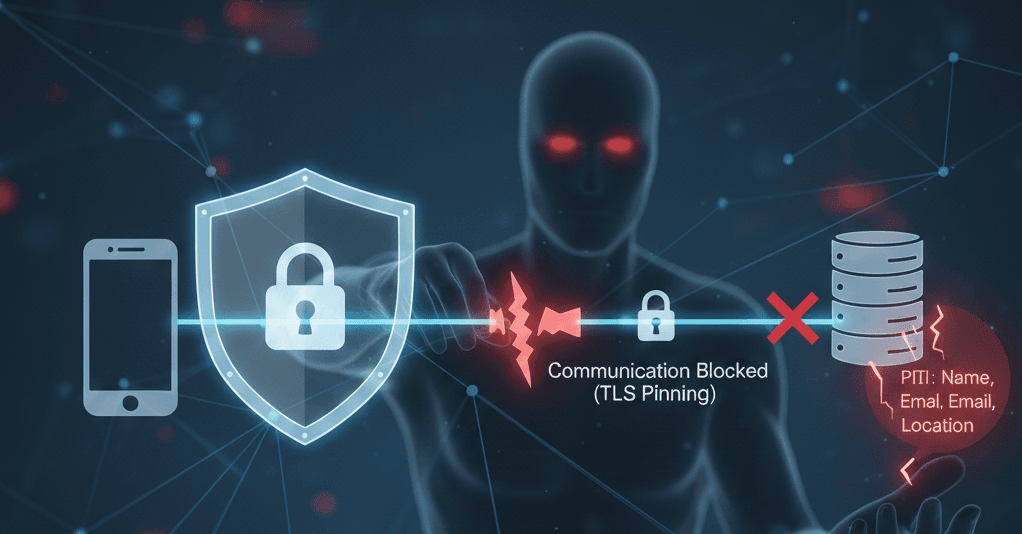
There's also Runtime Application Self-Protection (RASP), TLS Pinning, making sure you account for TLS bypass attacks.
Understanding mobile security also means knowing which tools the hackers use, so get familiar with MobSF, Frida, Ghidra, and Radare2. Be aware that like most topics, this is a rabbit hole from which you may never reach the end.
Other stuff you may want to brush up on:
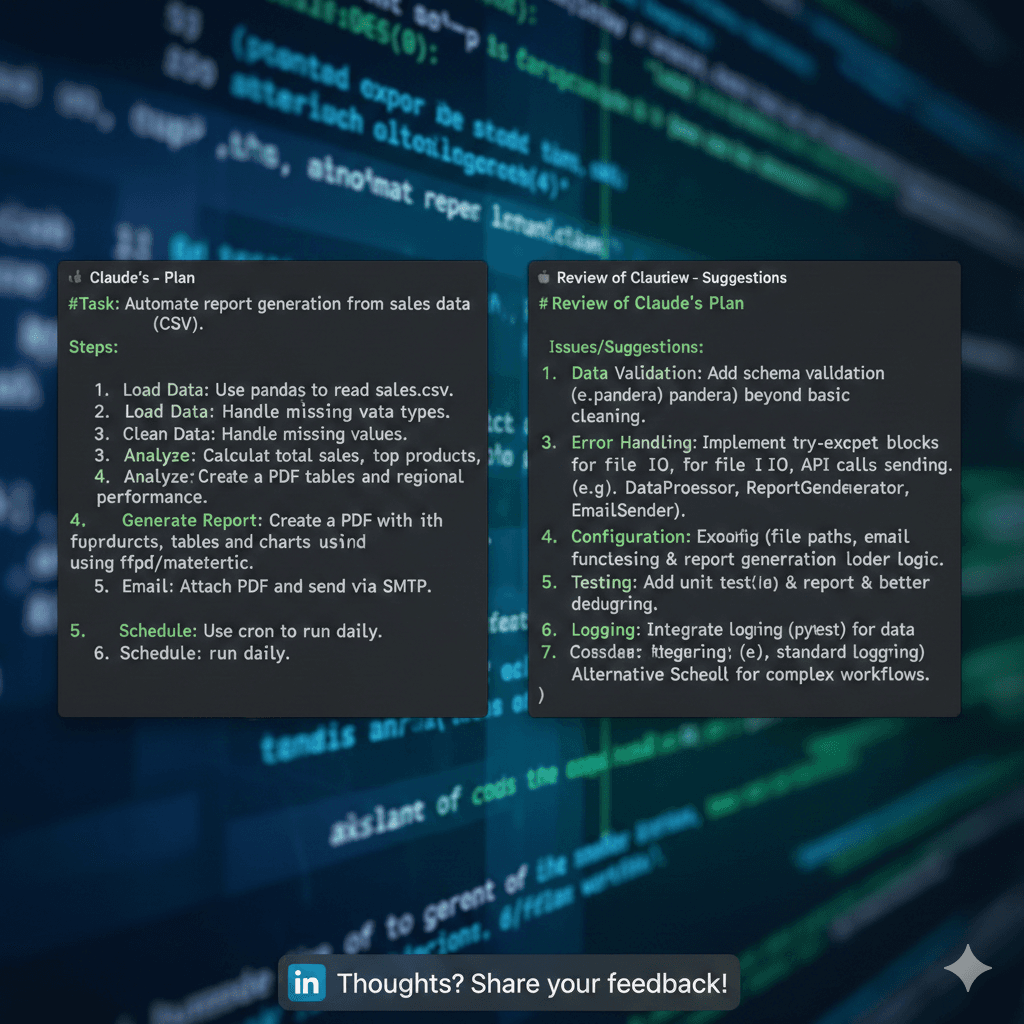
Data validation
User input sanitation
Data categorization (PII, public, private, classified, export controlled, etc)
Data retention
Privacy cover screen
Secure text fields
API documentation (defining maximum lengths, allowed characters, date formats, integer ranges, nullable fields, etc)
Memory safety
Objective-C method swizzling
AppDelegate swizzling
Red Team / Blue Team
Make sure to also watch security forums, read up on all the latest zero-days. Hackers keep innovating and discovering new ways to compromise our systems so we have to find new ways to defend our apps!
Go blue team!